AWS IAM Tutorial – Functions & Uses of Identity and Access Management
Free AWS Course for AWS Certified Cloud Practitioner (CLF-C01) Start Now!!
In our last session, we talked about what is Amazon WorkMail. Here, in this AWS IAM Tutorial, we will discuss what is Amazon IAM (Identity and Access Management). Moreover, we will study the functions and uses of AWS IAM.
So, let’s start the Amazon IAM Tutorial.
What is Amazon IAM?
AWS (Amazon Identity and access management) can help a user to manage to compute, store, manage, and application services in the AWS cloud. It uses access control techniques through which a user is familiar with which includes users, groups, and permission.
With the help of this, the user can specify the user and allow it to use specific services. This depends on the kind of action they perform with the help of the available resources. Amazon Cloudtrail helps to analyze and monitor the activities under process in Amazon IAM.
Microsoft directory can also be added using the federal based technology. This benefits IT, workers and managers, to monitor the services in a better way.
Do you know What is Amazon Cloudsearch?
With the help of a single AWS IAM, the user can manage the customer and their needs. It provides Amazon AWS building blocks which help the user to build the applications for the security purpose.
AWS Identity and access management help the user to focus on the features and functionality which includes the security on the other side of the things. AWS IAM can also rotate access keys on the virtual machine instances.
This makes sure that only the trusted user can access the AWS at any given time. Amazon IAM is economical and there are no additional charges for it. One can start using IAM very easily.
Functions of AWS IAM
Following are important Amazon IAM Functions, let’s discuss them one by one:
a. To Manage AWS IAM users and their access
The user will be able to produce users in Amazon IAM, assign them individual security. The user can also demand the temporary security credentials to produce users access to AWS services and resources.
Here, user will be able to manage permissions so as to manage those operations a user can perform.
Let’s explore the Essential Capabilities with Benefits of AWS Kinesis
b. To Manage Amazon IAM roles and their permissions
The user will be able to produce roles in AWS Identity and access management and manage permissions to manage that operations are performed by the entity, or AWS service, that assumes the role.
The user will be able to conjointly outline the entity is allowed to assume the role. Additionally, the user will be able to use service-linked roles to delegate permissions to AWS services that make and manage AWS resources on The user are behalf.
c. To Manage to federate users and their permissions
The user will be able to alter identity federation to permit existing identities (users, groups, and roles) in The user are an enterprise to access the AWS Management Console, decision AWS APIs, and access resources, while not the necessity to make an IAM user for every identity.
Use any identity management resolution that supports SAML 2.0, or use one in all our federation samples (AWS Console SSO or API federation).
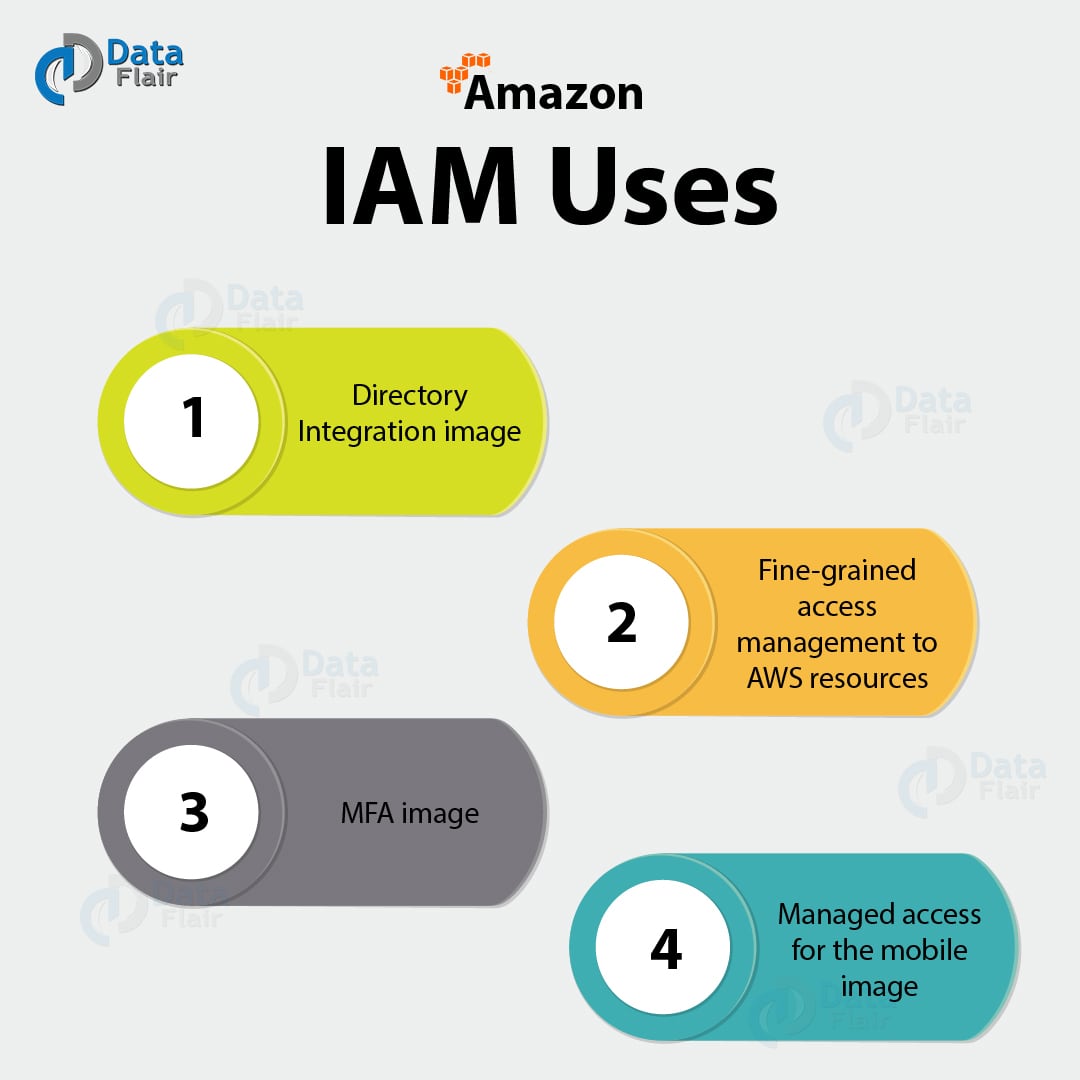
Amazon IAM Uses
Here, we will clear the Applications of AWS IAM in detail:
a. Directory integration image
AWS IAM is accustomed grant the user staff and applications united access to the AWS Management Console and AWS service APIs, using the user existing identity systems like Microsoft Active Directory.
The user will use any identity management answer that supports SAML 2.0, or be at liberty to use one in every of our federation samples (AWS Console SSO or API federation).
b. Fine-grained access management to AWS resources
Amazon IAM permits the users to regulate access to AWS service Apis and to specific resources.
IAM also permits The user to feature specific conditions like time of day to regulate however a user will use AWS, their originating science address, whether or not they are using SSL, or whether or not they have genuine with a multi-factor authentication device.
c. MFA Image
Multi-factor authentication for extremely valuable as it protects The user are AWS surroundings by using AWS MFA, a security feature out there at no further value that augments username and countersigns credentials.
Amazon MFA needs users to prove physical possession of a hardware MFA token or MFA-enabled mobile device by providing a legitimate MFA code.
d. Managed access to the mobile image
Manage access control for mobile applications with net Identity suppliers.
The user can modify the mobile and browser-based applications to firmly access AWS resources by requesting temporary security credentials that grant access solely to specific AWS resources for a configurable amount of the user’s time.
So, this was all about AWS IAM Tutorial. Hope you like our explanation.
Conclusion
Hence, we saw AWS helps the user to make their business better by providing the techniques. With the help of Amazon IAM, the user can create and manage AWS groups and users. It is also preferred as it provides the security benefit and the user can allow and deny them access to AWS resources.
Amazon Identity and Access Management does not include any upfront cost and is economical too. Furthermore, if we miss something or you want to share some information with us, feel free to ask in the comment section.
Did you know we work 24x7 to provide you best tutorials
Please encourage us - write a review on Google